Today’s news is full of stories about increased cyber-threats in NZ – Cyber attacks against Kiwibank, ANZ, NZ Post, MetService – experts see lockdown link – NZ Herald
We’ve seen several days of issues caused by these “DDOS” attacks.
Overnight, another cyber-threat snuck through
It is a zero day exploit of Microsoft MSHTML Remote Code Execution Vulnerability.
This is in the cyber security news because the exploit has a CVSS (Common Vulnerability Scoring System) of 8.8 out of 10 and impacts almost every Windows desktop, laptop and server.
As with all security alerts, this is an evolving situation.
Here are some things you need to know, as we currently understand them to be.
The exploit is active, hackers are using it right now to gain access to systems.
The news mentions Internet Explorer. You may think that because you use Edge or Chrome, you are not at risk. Unfortunately, that’s not true. Internet Explorer is still installed on almost every Windows device and hackers can exploit that. That’s even if you don’t actively use it.
Microsoft’s official workaround at this stage is to disable the installation of new Active X controls. This has a risk for some businesses which use applications that rely on these controls.
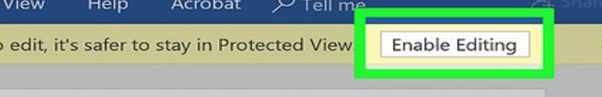
It is reported that delivery of the hack is through documents from the web. Infected documents have this malicious content hidden in them. The good news is that the default setting in Word is to disable this content for any documents opened from a web location. This is typically shown as the Enable Editing button on web documents.
You are least at risk if you have :
- Up to date Anti-Virus/EDR (Endpoint Detection and Response),
- All your Microsoft patches are up to date, and
- Use Multifactor Authentication (MFA).
Awareness is also a key tool in prevention. Please remind all your staff of the dangers around documents.
Don’t panic if you have Kinetics for KARE Security: Our Kinetics KARE for Security Clients already have these layers of protection, and KARE for Security S2 clients also have advanced EDR on all covered devices.
We expect that Microsoft will release an update to resolve the issue. In the meantime, everyone needs to take care accessing documents from emails and web sites – even more so than usual.
If you wish to follow Microsoft advice of disabling Active X, then Kinetics can use KARE to implement this on all devices for all devices covered under your agreement. This is chargeable for our Ready Reaction and Core Fundamental clients.
We recommend this as a temporary change as some line of business application make use of these controls. Kinetics is offering to deploy the Active X block across all end user devices and Remote Desktop Servers, then remove it once a fix is deployed at a fixed fee of $299+GST. This does not include any remediation if issues arise from any software like Line-Of-Business applications. If you wish to use this, please contact your account manager.
