There’s more than one infection going on right now. There’s an avalanche of cyber-criminal activity as well – the crooks are faking websites to look like official WHO ones, sending fake emails that appear that to come from authorities – health departments, doctors etc. Some will have files, either pretending to have relevant information or forms that, at first glance, seem reasonable.
But have your radar turned on! Be really cautious. Hackers are using these fake emails to wreak havoc. They realise that people are so uncomfortable now that they have lowered their guard on cyber-crime. Some of these documents are designed to gather information that will later be used in social engineering hacks against you, others simply contain malicious code that will spread malware onto your computer, and maybe even ransomware.
Be especially aware of old Office documents – .DOC, .XLS or .PPT. These are more vulnerable than most. Clients on KARE for Security can be confident their emails are being scanned with the ATP tool (advanced threat protection) that tests the documents, but nothing is fool proof.
Furthermore, these are setup on your business email accounts, whereas in this work-from-home world that we’re now in, often the same computer will also be collecting personal email accounts as well – and they have no such security in place.
In fact, home PCs are often poorly protected compared to business ones.
We’re also being told by the likes of Netsafe that, with kids being online for school work etc, we need to more alert than ever. Child predators are taking advantage of the situation to ‘groom’ kids and teenagers who are online more than normal now, especially while you are busy working form home and unable to supervise as closely as usual.
Remote working is here to stay, its becoming the new normal, so we have to get good at it. Organisations that do it well will beat those that don’t.
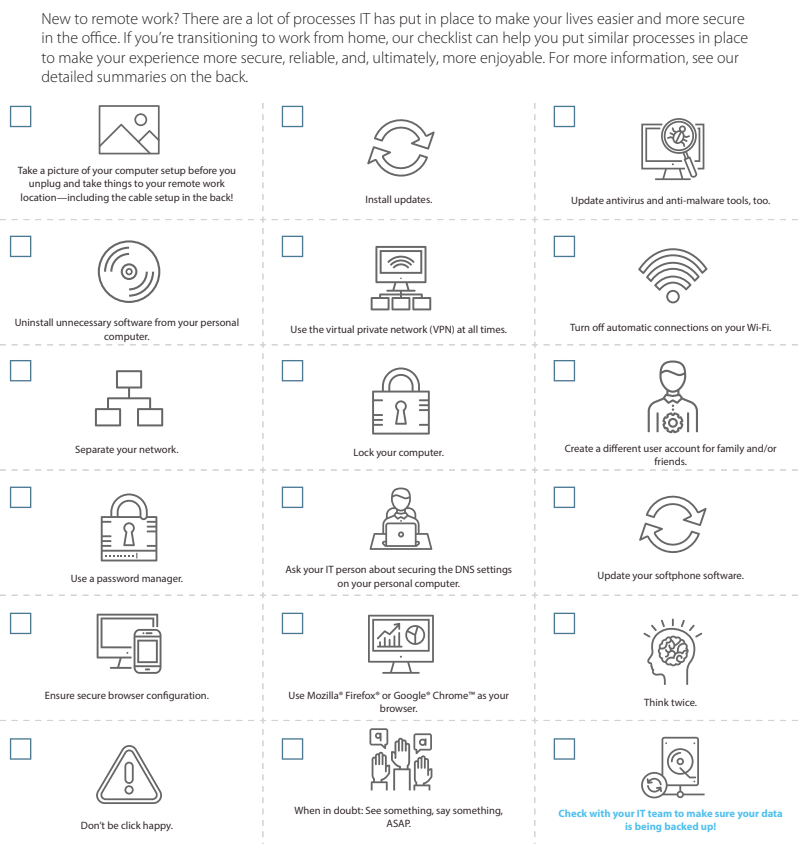
Here’s a simple remote working security check list to help you keep safe:
1) Take a picture of your computer setup before you unplug and take things to your remote work location—including the cable setup in the back!
At home, your tech won’t be with you to reconnect everything. A quick picture of where things are plugged and arranged may save you hours of frustration later. And don’t forget to use an approved cleaning agent to wipe things down before you disconnect.
2) Install updates.
Particularly if you’re working from a computer you already own but don’t typically use for office work, please check that all updates and patches to Microsoft®, Adobe®, and other critical software applications have been installed. We know, updates take time, and it’s all-too-convenient to click ‘Remind Me Later.’ However, many vulnerabilities exist in out-of-date software and are the perfect entry-point for a hacker. You must protect the data that you are entrusted to access. Keep it safe by ensuring your software is up to date.
3) Update antivirus and anti-malware tools, too.
As a follow up to number two, this may sound obvious. These tools are highly valuable and are designed to reduce risk and keep your computer safe from threat actors that want access to your company’s data. However, just like your office tools, it’s easy to postpone those time-consuming updates—ultimately leaving you at risk. If you’re using a home computer for your work and do not have a paid-for antivirus and anti-malware solution, ask Kinetics for help installing a licensed, approved corporate security software to use while working remotely.
4) Uninstall unnecessary software from your personal computer.
If you are using a personal computer, please uninstall software that isn’t being used by your family. Software that isn’t being used usually isn’t being updated or patched. Those patches prevent hackers from entering through known vulnerabilities. By removing unwanted or unused programs, you have reduced that risk.
5) Use the virtual private network (VPN) at all times. (if you use one)
We understand that it’s just one more thing that you need to do before you can work. Think of it as your seatbelt when you get in the car to drive. That extra moment it takes could be the moment that saved your office network from an attack. And don’t forget to re-engage the VPN every time you log on. It’s easy to put your computer to sleep when you walk away to grab lunch, forgetting that you’ve logged on to the VPN.
6) Turn off automatic connections on your Wi-Fi.
One easy way for hackers to gain access to your computer is Wi-Fi spoofing. For example, let’s say you routinely connect to ‘Joe’s Wi-Fi,’ so much that to save time, you click the button that says, ‘Connect Automatically.’ A hacker can set up a portal called ‘Joe’s Wi-Fi,’ and your computer may unwittingly connect automatically to that portal because it has been identifed as a safe network.
7) Separate your network.
When possible, connect your computer to a different network than the rest of your remote location. It may be as simple as using the company VPN to create that secure connection. If you are more technically capable, then separate your company computer from the rest of the computers in your remote work location via a different router or firewall. If your mobile data plan allows for unlimited data, consider using the hot spot on your phone instead of a guest network or your home network.
8) Lock your computer.
When you aren’t using your computer, just like at the office, lock the computer to keep family from accessing your company data. And while you are thinking about computer use, please remember that your company computer is for business use only. While it might be convenient to check the news or watch videos, please limit personal use and do not allow friends and family to use your work computer. Something as simple as a local restaurant’s menu could end up being a malicious file that exposes your computer to malware.
9) Create a different user account for family and/or friends.
If you plan to use your personal computer for remote work, create a separate user prole for you that is different than your other family members or friends. This is a major step towards helping the company meet our cybersecurity objectives.
10) Use a password manager.
If your company offers a password manager (like the new Kinetics KARE Password Vault), please don’t forget to use it to create and store passwords. The goal is to avoid saving passwords in the browser that can be easily stolen. We know sometimes it is easier to save it in the form or use the same passwords for different sites or forego using multi-factor authentication where it is offered. However, sacrificing the convenience is well worth it to avoid a security incident and loss of data. Remember that using a spreadsheet to save your passwords isn’t much better than saving them in the browser forms.
11) Ask your IT person about securing the DNS settings on your personal computer.
They should have the software or a tool you can use on your home computer that will test and curate URLs and help keep you from accidentally going to the wrong places.
12) Update your softphone software.
If set up correctly, softphones, like voice over IP (VoIP), can be very convenient. However, if they are not secure, they can be exploited fairly easily by cyber criminals. If you are using a softphone system at home, make sure you are taking active preventative measures to avoid hacking.
13) Ensure secure browser configuration.
Google Chrome extensions can be a hotbed for computer viruses. It’s best not to use them at all. However, at the very least, make sure those you are not using are uninstalled. If you’re not sure how to do this, ask your IT professional.
14) Use Microsoft Edge, Mozilla Firefox or Google Chrome as your browser.
Many other browsers can contain vulnerabilities that can open you up to a variety of cyberattacks, ultimately leaving company data exposed. Edge, Firefox and Chrome have the most up-to-date security.
15) Think twice.
The threat actors, also known as cyber criminals, are looking to take advantage of you when you least expect it. Right now, receiving an email that looks like it came from your boss or CEO with a subject line that reads, “Company Coronavirus Update” may seem normal, but it may not actually be from your company. Take a moment to review who it came from (the actual email address, not the name in the display). Also, question whether this person would typically send you an email like this.
16) Don’t be click happy.
Just because there is a link or an attachment does not mean that you need to click. Mouse over the link and see where it wants to take you. Check for the actual spelling of the domain in the area before the .com, .net, .edu, .gov, or .org looking for anything unusual like the characters ‘1’, ‘l,’ or ‘I’ being leveraged as an imposter domain. Another example would be the letters ‘rn’ instead of ‘m’ or ‘vv’ instead of ‘w.’
17) When in doubt: See something, say something, ASAP.
You are a human firewall, the first line of defence against threat actors trying to invade the network. While we know you will never click on a fake email, in the event anything odd seems to have happened, we’d rather know about it than ignore it and hope it goes away. If you may have done something that afterward, seemed suspicious, let us know as soon as possible. And if you accidentally did something that later you realised was bad, disconnect your computer from the VPN and network and call us right away.
18) Check with your IT team to make sure your data is being backed up
Make sure your files are where they should be, and there is a service like KARE operating that backs these files up for you.
(Content thanks to ConnectWise | 4110 George Rd., Suite 200 Tampa, FL)